About Whoa TOPS
After focusing on the delivery of the Whoa Customer Portal, one of the biggest questions for Whoa was “What are we really protected from?” For Whoa, where data security is the key tenant of their business offering, this was something they wanted to address as visibly as possible. In order to provide visibility to its customers, Vaporware designed and developed a Threat Detection display that could be used for real-time or reporting purposes on world-wide cyber attacks on Whoa systems. This information could be accessed as a map on desktop or as a report on mobile.
Coined TOPS, the Threat Observation Platform was a unique way to visualize and analyze the security provided to your public cloud. Before TOPS, executives didn’t understand their IT departments’ spend on security products, instead relying on a black box of IT professionals to ensure their safety. With TOPS, executives can see a live dashboard of blocked fraudulent traffic and international attacks to convey trust and safety to their leadership teams.
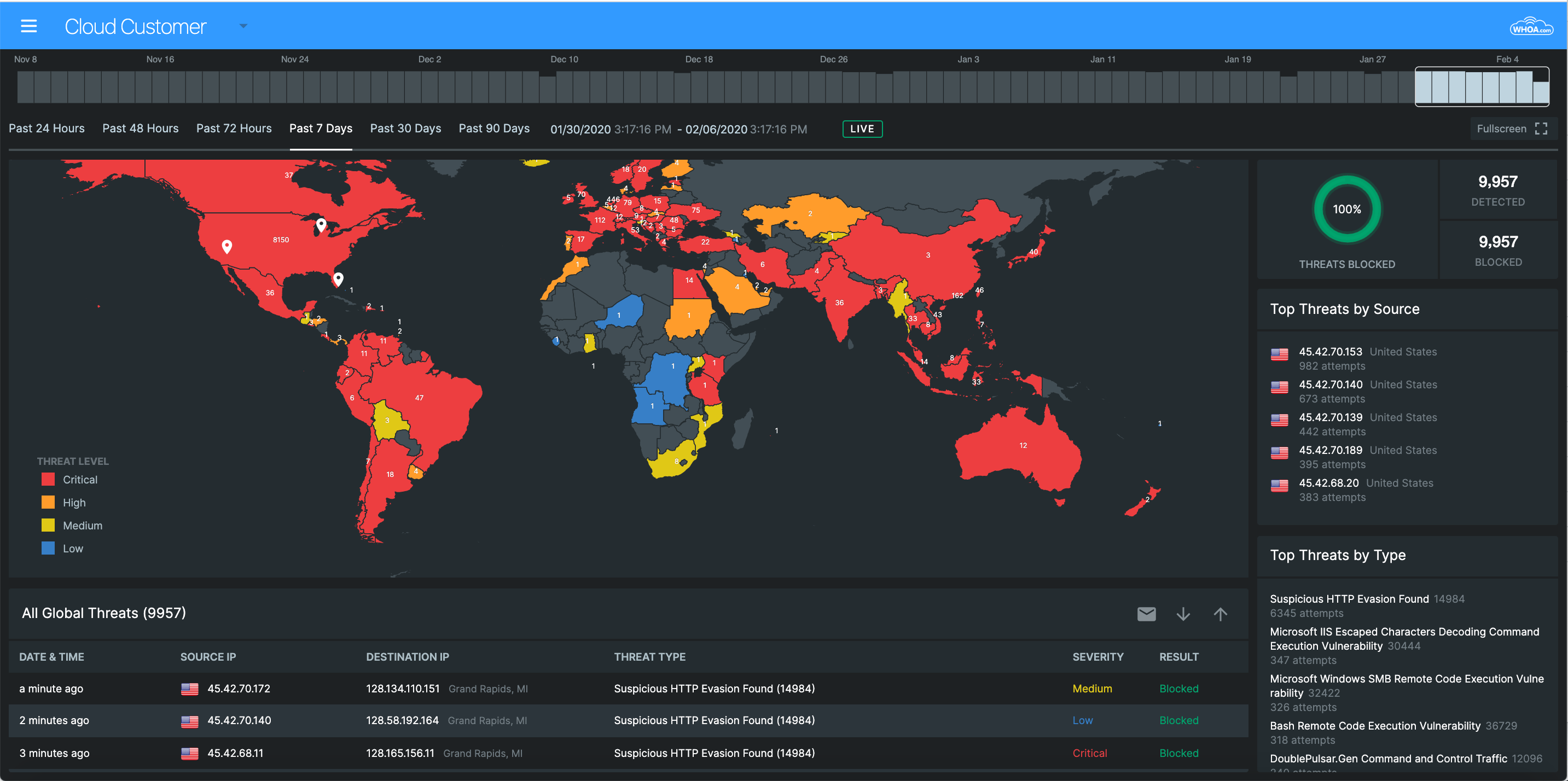
The main TOPS dashboard view. Allows the user to change the date range to see threats within the last 90 days.
Real-Time Reporting
The TOPS dashboard offers many advanced features that allows an analyst to view threats data in different ways. In addition to a live view of incoming threats that is updated in real time, specific date ranges in the last 90 days can be specified. Individual countries can be clicked in order to zoom in and see only threats originating from that country. Top threats by source and type are shown for any selected filters. Last but not least, a log of the threats can be emailed in report form for further analysis.
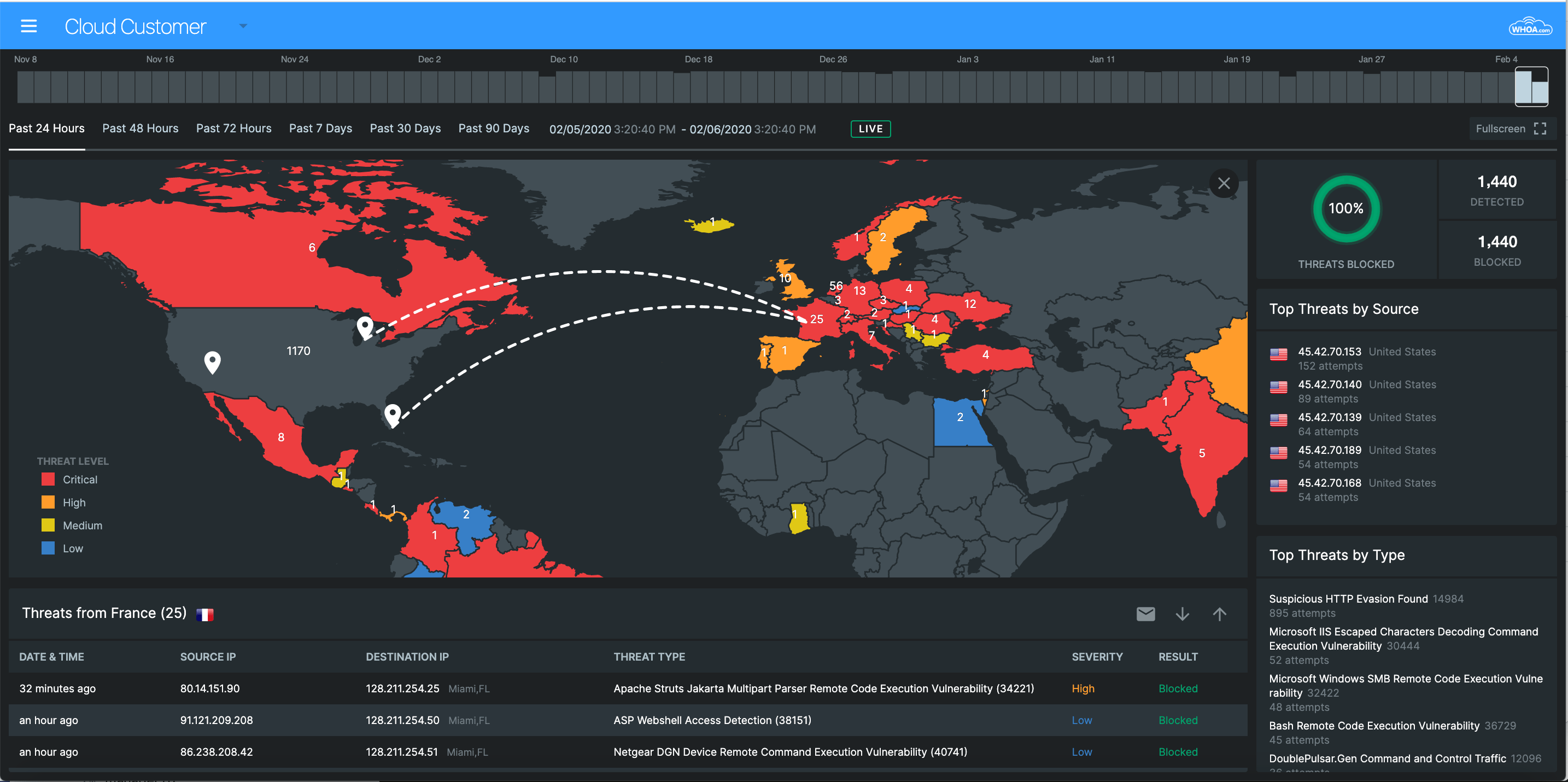
Click on a country to zoom in and get specific threats originating from there.
Mobile Experience
The TOPS platform had to support both mobile phone and tablet experiences for executives and analysts looking to view threats data on the go. We were able to include these responsive views using a single codebase, saving time and money.
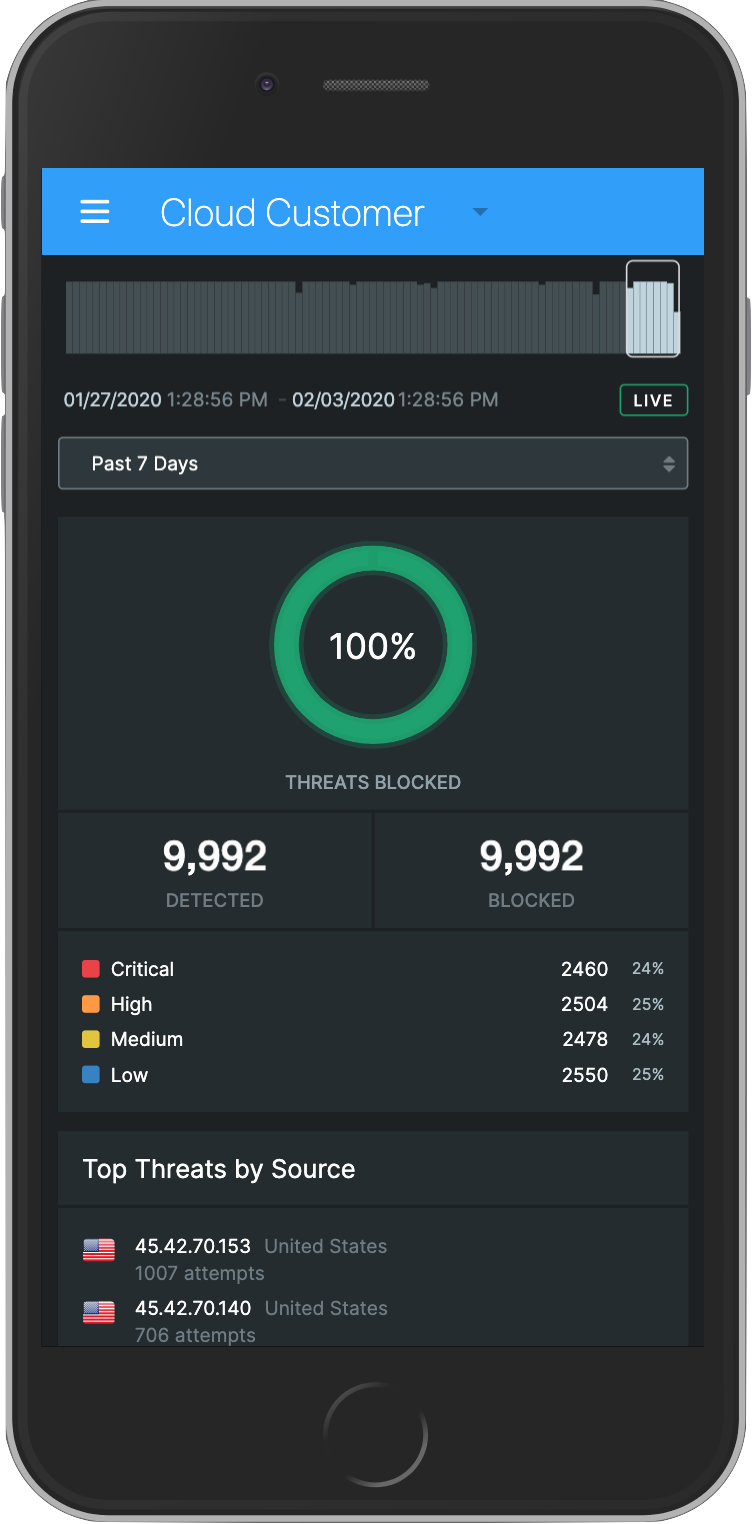
The mobile experience has all of the functionality of desktop except for the map view.
Final Thoughts
The Whoa TOPS platform has become a valuable addition to Whoa's managed hosting and cybersecurity offerings. It allows them to offer a distinctive service and experience to differentiate themselves in a crowded market.
